Asking what is a group key rotation interval means that you’ve dug quite deep into the processes that are barely noticeable because they’re happening in the background and they’re in the shadow of much larger things.
The group key rotation interval is something that happens on a wireless network where there are over two devices connected. It’s a security method, and to understand it, we need to discuss the necessity of wireless security, the protocols, and how group key rotation works.
CONTENTS
The Necessity of WI-FI Security
If there was no threat, WI-FI security protocols wouldn’t have been invented. However, there are genuine threats out there that can exploit our wireless connection to do serious damage to our devices and others. Here are some scenarios:
- MITM attacks: Aka man-in-the-middle attacks are instances where someone can change the message from you and your closest friend if they’re skilled enough, and this can cause a serious misunderstanding.
Man-in-the-Middle Attack
- Data manipulation: If there was no WI-FI security, there would be many opportunities for someone to manipulate the data on your devices without you knowing until you notice someone tampered with some frequently used files.
- Packet sniffing: Packet sniffers are software used to analyze data packets coming in and out of your network. Although these are mainly used for good things like fixing issues regarding some services, e.g. email, browser apps, etc.
What is Packet Sniffing
- Password decryption: There are tools like password decryptors, but hackers can use your unprotected network to decrypt your passwords. Accounts like PayPal, your online banking account, etc.
WI-FI Security Protocols
One of the more significant reasons we need WI-FI security protocols is that we don’t want someone accessing our home network, viewing the devices connected to it and if skilled enough, messing with the configuration, that’s why these four protocols were developed:
- WEP: Wired Equivalent Privacy offered data confidentiality equivalent to a wired connection. Hence, the name. However, this protocol is probably no longer used by anyone as it has been superseded by the WPA.
- WPA: WI-FI Protected Access was created by the WI-FI Alliance to replace the WEP because of security issues. This was only a temporary solution to the security issues WEP faced, and they built it just to sustain security until they developed WPA2.
- WPA2: This protocol needs the user to use the SSID and the password so an encryption key would be generated for the device, and the user would connect said device to the network with that unique key.
- WPA3: The final security protocol that grants access without the necessity of sending the password wirelessly to the device. This eliminates the possibility of someone grabbing the password remotely and entering your wireless home network.
Our Recommendation for Wireless Security
There are different tips and tricks you can use on your wireless network to improve its security. These can apply to home networks or company WI-FI networks, and some steps might require you to log into your router. Do this, and you can feel much more secure:
Turn Off Wireless Admin Access
Nobody should be able to access your router’s settings wirelessly, especially if you haven’t changed your default username and password. All routers come with default usernames and passwords.
When you allow wireless admin access, almost anyone connected to your WI-FI can enter the admin settings of your router and tamper with them. Apart from changing the SSID and password, they could control how much data gets through to or from you.
SSID That Doesn’t Stand Out
Try not to use a network name that stands out, because you can become an easy target. When running a business, stick to the generic name of the router instead of using the brand name. This way, the network remains secure as it’s not that distinct from most detectable networks.
It’s also recommended to keep the generic name of the router through which you provide wireless access to your employees. When you’re at home, you can detect the networks and try to come up with a name that wouldn’t stand out so much from the group.
Try Not to Use WPS
WI-FI Protected Setup is an insecure method of connecting devices to your wireless network. It’s a synchronization where your router sends out a signal with the key, and the device you’re pressing the button on receives the signal and the key.

Thus, the device is now connected. But almost anyone can connect this way, and this makes it far less secure than other methods of connection. If there’s an option to disable the WPS button, do it.
Multiple Networks
Finally, if you’re running a business, keep the company network and the publicly accessible WI-FI separate. Further, keep the company network secure and inaccessible to the public, i.e. don’t give out the password.
Make it a company policy not to share the password with unauthorized personnel. This should be a policy in every major company, as it is essential that confidential data remain confidential.
What Are Group Keys?
One of the integral parts of WI-FI security is the Group key. The router distributes these keys to all the devices connected to the wireless network. The router handles group key distribution, and they’re necessary because:
- They eliminate the need for the router to send copies of data to all devices.
- There’s no need to pair every device with the router separately.
- Instead, the router simply broadcasts the original data to all the devices.
- Each device relies on the group keys to receive the messages.
- Group keys help encrypt the data, but there are different types.
How Does Group Key Rotation Interval Work?
We’re going to describe how this works in steps. It starts with key distribution, and there’s a necessity to create a GMK (Group Master Key) and use the GTK (Group Temporal Key) to get the GEK (Group Encryption Key) and the GIK (Group Integrity Key).
Instead of overcomplicating the situation, we’re going to tell you that all these keys change according to the configuration of your router. So, it makes it nearly impossible for a device to communicate within the network without performing this 4-key handshake.
How Does This Reflect on Your User Experience?
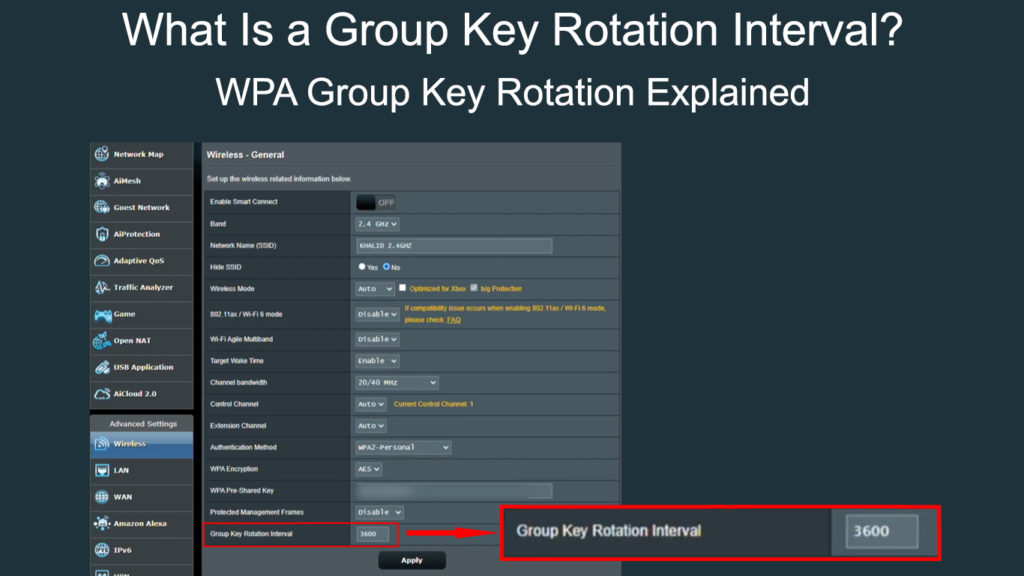
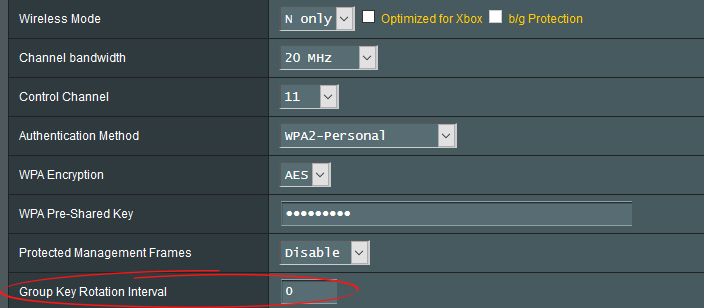
Well, added security is always a plus and, with most routers, you can change the group key rotation interval. You can set it to any period you think might work for you best. However, your devices will experience a disconnection once that time passes.
Now, the key gets generated by your router automatically, and once the key is refreshed, you won’t have to enter a new password. The key doesn’t change the password, therefore automatic reconnection is possible.
There is one instance in which the group key interval should be set to 0. When you have WI-FI extenders in your home. Then, set the extender’s group key interval to some value. It’s best to leave the setting unchanged.
Conclusion
Wireless security is necessary because there have been many reported cases of breaches and attacks. There are several WI-FI security protocols in play, and there’s the group key rotation interval that gives us even more security. Don’t mess with the setting if you don’t need to, and if you do, feel free to set the interval to as low or as high as you’d like.

Hey, I’m Jeremy Clifford. I hold a bachelor’s degree in information systems, and I’m a certified network specialist. I worked for several internet providers in LA, San Francisco, Sacramento, and Seattle over the past 21 years.
I worked as a customer service operator, field technician, network engineer, and network specialist. During my career in networking, I’ve come across numerous modems, gateways, routers, and other networking hardware. I’ve installed network equipment, fixed it, designed and administrated networks, etc.
Networking is my passion, and I’m eager to share everything I know with you. On this website, you can read my modem and router reviews, as well as various how-to guides designed to help you solve your network problems. I want to liberate you from the fear that most users feel when they have to deal with modem and router settings.
My favorite free-time activities are gaming, movie-watching, and cooking. I also enjoy fishing, although I’m not good at it. What I’m good at is annoying David when we are fishing together. Apparently, you’re not supposed to talk or laugh while fishing – it scares the fishes.
