We can all agree about privacy being one of our top priorities when we are online. Whether you are a school student, an employee, or a tourist, you want to be sure no one can get to your texts and other private digital possessions when you connect to the Wi-Fi network in a school, workplace or some random public place. Many of us asked ourselves one or more of the following questions:
Can a teacher read my texts about mocking him when I’m connected to a school Wi-Fi?
Is there a way for the boss to find out I hate him and my job when I go online using a wireless connection at work and share my thoughts and feelings in a chat?
Is it easy for some hacker to read my screen and steal my data while I’m walking across a public square, chatting over a public Wi-Fi network?
Can my partner go through my messages at home without taking my phone, but exploiting the fact that we both share the same network?
The short answer is – mostly NO. However, it can be done using some reacharounds.
If you want to learn how and why, what are the exceptions, and what needs to be done in order to read someone’s texts or screen contents, keep reading to the end of this blog.
CONTENTS
How Are Your Texts Protected from Hackers When You Are Online Using Wi-Fi?
Mobile phone users send two types of text messages.
One is SMS (Short Messages Service) or MMS (Multimedia Messages Service) and the other are chat messages exchanged via some popular programs and platforms (Viber, WhatsApp, FB messenger etc.). PC users mostly use the latter.
SMS and MMS messages are transferred using a mobile signal, and their vulnerability has nothing to do with whether you use Wi-Fi or not.
Most chat apps and services use end-to-end encryption (E2EE). This means your messages get encrypted on your phone before being sent. They remain encrypted all the way to the end user’s device, where they are being decrypted back to the readable text.
How Can Someone Read My Texts?

In order to read messages transferred using end-to-end encryption, an attacker must (1) either find a way to install some spy or remote control software on your phone, (2) intercept and then decrypt messages somewhere between the end-users, or (3) find a way to mimic the end-user, decrypt and read the message, then forward it to the end-user in order to avoid detection.
Let’s go from the top.
1. There are many remote access software solutions like AnyDesk, TeamViewer, and others. But, to exploit them, an attacker needs to install them on your device and then allow connection with his device without you noticing it. If he somehow succeeds, he can pretty much see your screen and everything you do in real-time. He can even take over and control your device like his own. However, this has nothing to do with you being on the same Wi-Fi or not, or with you using Wi-Fi at all. This will work as long as you are online using any kind of internet connection.
Another type of software that can be used to read your texts is a keylogger. Keyloggers can be both hardware and software.
The hardware version is a little device that plugs into your laptop or computer. It intercepts signals from your keyboard and stores them in internal memory or relays them to the attacker. These kinds of attacks are more likely to happen if you often use the same, publicly accessible computer in an internet café or library because the attacker needs to plug the device into the victim’s computer.
Software keyloggers can be sent to the victim as attachments or hidden within some other file, but most security software will detect them and warn the user before letting them be installed. However, an unaware user can allow the installation manually, thus giving the attacker access to all the keyboard inputs.
2. Even though being on the same Wi-Fi network can make intercepting encrypted messages a tiny touch easier, decrypting them is not an easy task. It requires very sophisticated hardware, software, and it is a time-consuming process. Unless you are on the most wanted list, there is very little chance you will have to deal with this kind of privacy invasion.
3. Mimicking the end-user to get a decryption key is also one of the options to get your texts. This method is also known as Man-In-The-Middle (MITM). However, most of the end-to-end encryption protocols use some kind of endpoint authentication to prevent these kinds of attacks.
Also, it is worth mentioning that some of the less popular messenger services don’t use end-to-end encryption. This makes communication through them easy prey for the attackers.
How Can I Protect Myself When I’m Sharing Wi-Fi with Unknown People?
There are a few simple things you can do in order to stay safe from unwanted people getting access to your device, chats, texts, and other private data.
Never leave your device unlocked and unattended.
This will prevent anyone from gaining physical access to your phone or computer, allowing him to bypass the security and install spy or remote control software. Use good, reliable VPN software.
A Virtual Private Network or VPN is a piece of software that virtually creates a private network. Using it, all your communication with the internet goes through an encrypted tunnel, making it very difficult to hack.
Pay attention to the icon of the lock on the left side of your browser’s address bar.
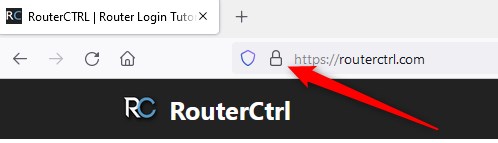
If it shows unlocked, don’t download anything and totally avoid it if possible.
The lock icon shows whether the website you are visiting has an SSL certificate or not. SSL stands for Secure Socket Layer. This protocol allows secure, encrypted communication between your browser and the server.
Summary
Even if using the same Wi-Fi network doesn’t allow the owner to access your private data or read your texts, it can make you vulnerable to attacks. In order to prevent this, you can follow a few simple pieces of advice. First, don’t leave any of your devices unlocked and unattended.
When you are connecting to the internet, use VPN software. Communicate through services that use end-to-end encryption like Viber, FB messenger or similar and avoid downloading files or interacting with websites without SSL certificates represented by a locked lock icon on the left of your address bar.

Hey, I’m David. I’ve been working as a wireless network engineer and a network administrator for 15 years. During my studies, I also worked as an ISP field technician – that’s when I met Jeremy.
I hold a bachelor’s degree in network engineering and a master’s degree in computer science and engineering. I’m also a Cisco-certified service provider.
In my professional career, I worked for router/modem manufacturers and internet providers. I like to think that I’m good at explaining network-related issues in simple terms. That’s exactly what I’m doing on this website – I’m making simple and easy-to-follow guides on how to install, set up, and troubleshoot your networking hardware. I also review new network equipment – modems, gateways, switches, routers, extenders, mesh systems, cables, etc.
My goal is to help regular users with their everyday network issues, educate them, and make them less scared of their equipment. In my articles, you can find tips on what to look for when buying new networking hardware, and how to adjust your network settings to get the most out of your wi-fi.
Since my work is closely related to computers, servers, and other network equipment, I like to spend most of my spare time outdoors. When I want to blow off some steam, I like to ride my bike. I also love hiking and swimming. When I need to calm down and clear my mind, my go-to activity is fishing.

Could you please expand a bit more on this?
“SMS and MMS messages are transferred using a mobile signal, and their vulnerability has nothing to do with whether you use Wi-Fi or not.”
In my situation I left my phone connected to someone else’s Wi-Fi for about a week. I am afraid this someone read or will be able to read my messages from then on. This someone works on IT security, and the messages are regular carrier messages (not through an app). Also the owner of the Wi-Fi has not had access to my device at all.
Do you think this person was able to access my carrier text messages?
thank you so much! this is a very informative publication.